Alike v6/A2 Documentation
Welcome to the Alike documentation
Configuration
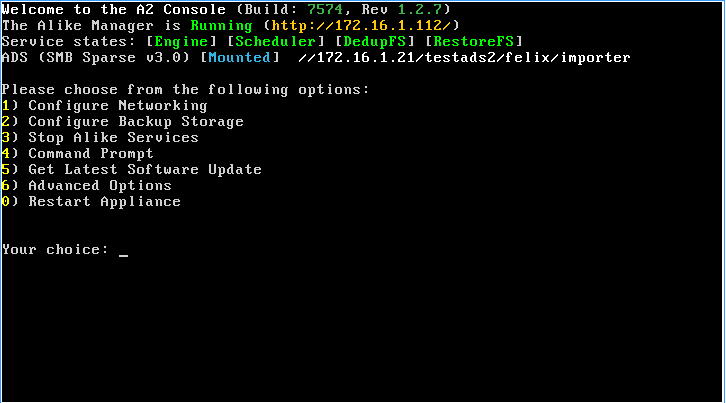
Once you have configured your A2 networking, and your backup storage (ADS) location, you can now begin managing your A2 from a web browser.
Simply point a (supported) browser at your A2's IP (seen on your A2 console: http://172.16.1.112 )
Here you can login with the default credentials:
- Username: alike
- Password: alike
Please change your alike password using the A2 console as soon as possible.
Note: Your "alike" user account will allow you to login to the following A2 services:
- SSH (console)
- Web (http)
- SMB (Restore Share and Job logs)
Initial Setup
When you login for the first time, you will be greeted with a mini-wizard to help you setup a few essential settings.
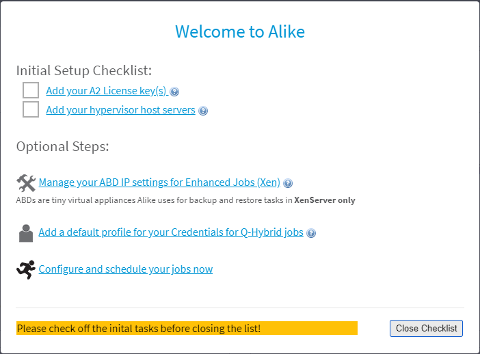
- Add your License keys
- Add your Hypervisor host servers
- Manage your ABD Network settings (for Xen/XCP customers only)
- Create a default Credential Profile (for Q-Hybrid jobs)
Adding License Keys
Alike keys come in 3 different editions: Free, Standard, and DR
Please Note: You cannot mix different edition keys on the same A2.
Installing your license key is as simple as pasting your key into the form shown, and clicking "Activate":
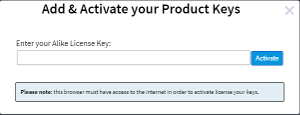
You will need an active internet connection (from your local web browser) in order to activate your license keys.
Please note: Once a license key has been activated on an A2, it cannot be reused. If you need to re-apply your license key after activation, please contact info@quadricsoftare.com for assistance.
Adding host servers
To add a host server, simply follow the link from the initial wizard, or navigate to: Systems->Manage Hosts in your Alike UI. Here you should add any hypervisor hosts that you wish to protect, or restore/replicate to. For Alike Standard/DR editions, you must "license" any host you wish to protect.
Please Note: Hosts that are only used for restore/replicate targets do not require licensing.
Manage ABD Network Settings
ABDs (Alike Backup Delegate), are a critical component for XenServer/XCP customers only. These tiny virtual machines perform much of the work for backup, replicate, and full VM restoration jobs. Understanding how they work is important to keep Alike running smoothly, and troubleshooting any problems that might arise.
ABDS Highlights:
- ABDs are Stored as a Template in your default SR
- Only 1 template is required per Xen Pool
- ABDs use DHCP by default
- ABDs require a XenNetwork that can communicate back to the A2's IP
- ABDs are provisioned on demand. Once an ABD is created, it will remain idle until needed again.
So, you should at minimum check your ABD XenNetwork to ensure the proper vlan is being used for your ABDs.
For more information on ABDs, please to the ABD overview.
Credential Profiles
Alike uses "Credential Profiles" as a convienent way to definte your authentication for Q-Hybrid and Physical systems. A Credential Profile is simply a defined username/password combination which can be applied to multiple systems. The first profile you add will automatically become your "Default Profile", and will be used for all Q-Hybrid jobs. You can create as many Profiles as you like, but only 1 can be your default. To assign a specific credential profile to a VM, simply navigate to that VM's settings under "System Explorer", then click that VM, (expand the settings if needed), and choose the Profile from the dropdown.
Setup your jobs
You are now ready to configure a job. Please refer to the section on the specific type of job you need:
In Alike, jobs can be scheduled or defined to run only when you tell it to (manual).
For Scheduled jobs, you can choose what days a job will run (eg. everyday, one or more days of the week, or even just a specific day of the month).
Furthermore, you can also specify how many times a job will run per-day. By default a job will only run once at the specified date/time, but this can be increased up to "every 15 minutes".
Lastly, you choose the hour and minute for the job to start.
These scheduling options are common to all Alike job types, but are generally only used for backup and replication tasks.